Security 3 - New EMV Cards
EMV cards are about to be rolled out massively in the US, so you heard it here first!
EMV Card
- EMV (Europay Mastercard Visa) have been in use in Europe for over 20 years (EMV on wikipedia)
- Known as "Chip and Pin" and "Chip and Signature" cards
- There are various attacks to nibble at EMV, but EMV is much more secure than the old mag-stripe system
- The terminology and available options are quite complicated, but the basics are simple
Mag-Stripe Credit Cards
- The old way - really quite insecure
- One "secret" is the Credit Card number, printed on the front of the card
- There's also a "CVV1" number on the mag stripe, not printed on the back
- There is a different CVV2 number printed on the back, used in web site type transactions
- You've been asked to type in CVV2 many times
- For a card-swipe transaction, the "secret" is the CC number + the CVV1 number
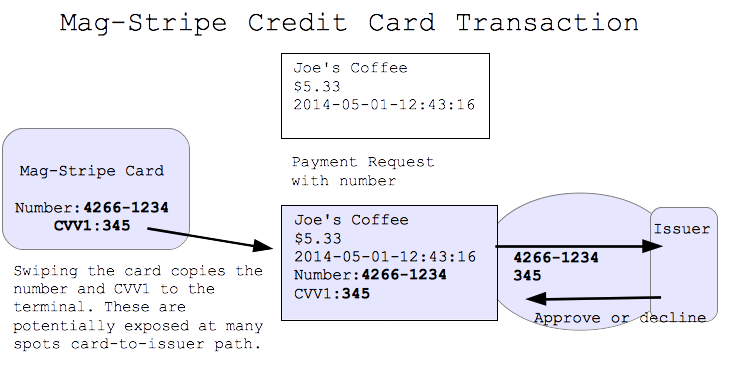
Mag-Stripe Credit Cards Weaknesses
- A "skimmer" is a device which notes down these secrets for use by bad guys later
- The "Target" store hack was basically a huge skimming operation
- a. Skimmer might be incorporated into the terminal
- b. The waitress walks off with your card, takes 10 seconds to run it through a skimmer
- The "secret" goes along the card-to-issuer path: card, to waitress, to terminal, ...
- We try to keep that whole path secure, but it's impossible to plug 100% of the leaks
- A terrible system by 2014 standards
EMV Chip on Card
- There's a chip on the card, the chip has a secret "key" on it (i.e. a password)
- Main point: the secret key never leaves the chip
- So even if the retailer's credit card terminal is compromised .. the secret is still safe
- The system uses keys and encryption
How EMV Works
- Insert the card chip-side up into the terminal, leave it in so it can communicate
- Merchant creates a payment request, sends it into the card
- The chip in the card creates with its secret a single-use encrypted blob payment request
- The merchant sends this to the issuer to request payment
- The request also includes the CC number, but not CVV1 (IMHO a design error)
- The encrypted blob is not much use to the bad guys if intercepted
- The secret never leaves the chip
- The architecture avoids needing 100% security along the card-to-issuer path
- I estimate EMV is about 100x more secure than mag-stripe for skimming

Key EMV Scenario: skimming
- What scenario does EMV solve?
- The "skimmer" scenario: you use your card in person somewhere, and bad guys makes a duplicate card
- EMV does not yet solve the on-the-internet scenario (they're working on it)
EMV Weaknesses
- EMV is not perfect
- EMV optionally supports a PIN, helps card-stolen case
- In the US, most issuers are not using PIN, avoiding credit/debit confusion
- Weakness-1. The encrypted blob exposes the CC number, but not CVV1, so it's mostly but not completely useless to bad guys
- PIN Weaknesses - Bad guys trick PIN out of you
- Weakness-2. Bad guys could, say, watch you typing to observe your PIN
- Weakness-3. Bad guys could create a fake terminal that records what you type and then says "service unavailable" to get your PIN
- EMV makes skimming hard, but simply stealing the card may work (depending on PIN)
- In the early days, some european issuers would stick customers with stolen EMV charges
- IMHO that was a policy error, and the US does not work that way
- If your card is stolen and you report it reasonably, your liability is technically $50 but typically $0
EMV Summary
- This is going to be a big improvement
- Addresses the skimming case
- There are weaknesses, but not fatal ones
- We might see PIN get rolled out in the USA eventually. That helps with the card-stolen case.
- Next we need to solve the "internet" case